CVE-2022-0847
Linux Kernel Privilege Escalation Vulnerability - [Actively Exploited]
Description
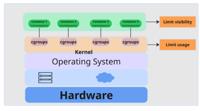
A flaw was found in the way the "flags" member of the new pipe buffer structure was lacking proper initialization in copy_page_to_iter_pipe and push_pipe functions in the Linux kernel and could thus contain stale values. An unprivileged local user could use this flaw to write to pages in the page cache backed by read only files and as such escalate their privileges on the system.
INFO
Published Date :
March 10, 2022, 5:44 p.m.
Last Modified :
Nov. 6, 2025, 2:50 p.m.
Remotely Exploit :
No
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Linux kernel contains an improper initialization vulnerability where an unprivileged local user could escalate their privileges on the system. This vulnerability has the moniker of "Dirty Pipe."
Apply updates per vendor instructions.
Unknown
https://nvd.nist.gov/vuln/detail/CVE-2022-0847
Affected Products
The following products are affected by CVE-2022-0847
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Update the Linux kernel to a patched version.
- Reboot the system to apply the kernel update.
Public PoC/Exploit Available at Github
CVE-2022-0847 has a 617 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2022-0847.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2022-0847 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2022-0847
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
An automated toolkit that scans a Linux system for privilege escalation misconfigurations. Built as a practical cybersecurity project covering red-team enumeration and blue-team auditing techniques.
Python Shell
Automated Linux Privilege Escalation Detection Toolkit for Security Auditing
Python Shell
None
C Makefile
A repository for my CPTS Preparation Notes
None
Shell Makefile C
old traitor with new exploits
Go C
dirtyfrag exploit poc
C
None
HTML Python C
None
Makefile Go PowerShell Shell Assembly C Python Rust HTML JavaScript
RootHawkX 是一个 Linux 本地安全测试终端工具,本项目基于RootHawk进行修改,集成了更多漏洞利用模块。
Go C Batchfile Shell
This is an automated cve scanner that helps look for vulnerabilities in systems.
HTML
None
Dockerfile C Shell HTML
None
None
Lab detection exercise for DirtyFrag (CVE-2026-43284) - Linux kernel privilege escalation via xfrm-ESP page cache corruption. Full write-up covering exploit execution, detection gaps, and corrected EQL rules using Elastic Stack
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2022-0847 vulnerability anywhere in the article.

-
Ars Technica
The most severe Linux threat to surface in years catches the world flat-footed
Publicly released exploit code for an effectively unpatched vulnerability that gives root access to virtually all releases of Linux is setting off alarm bells as defenders scramble to ward off severe ... Read more

-
The Hacker News
New Linux 'Copy Fail' Vulnerability Enables Root Access on Major Distributions
Cybersecurity researchers have disclosed details of a Linux local privilege escalation (LPE) flaw that could allow an unprivileged local user to obtain root. The high-severity vulnerability tracked as ... Read more
-
CybersecurityNews
Linux Kernel 0-Day “Copy Fail” Roots Every Major Distribution Since 2017
A critical zero-day vulnerability in the Linux kernel has been publicly disclosed, enabling any unprivileged local user to obtain root access on virtually every major Linux distribution shipped since ... Read more

-
Kaspersky
Exploits and vulnerabilities in Q3 2025
In the third quarter, attackers continued to exploit security flaws in WinRAR, while the total number of registered vulnerabilities grew again. In this report, we examine statistics on published vulne ... Read more

-
CybersecurityNews
Threat Actors Leveraging Windows and Linux Vulnerabilities in Real-world Attacks to Gain System Access
Cybersecurity teams worldwide have observed a surge in sophisticated campaigns exploiting both Windows and Linux vulnerabilities in recent months to achieve unauthorized system access. These attacks o ... Read more

-
Daily CyberSecurity
Kaspersky Report: Vulnerabilities Are Exploding, and Attackers Are Adapting
Kaspersky Labs has published its Q2 2025 vulnerability analysis, revealing an alarming rise in both the number of vulnerabilities registered and their exploitation in the wild. The findings show that ... Read more

-
Kaspersky
Exploits and vulnerabilities in Q2 2025
Vulnerability registrations in Q2 2025 proved to be quite dynamic. Vulnerabilities that were published impact the security of nearly every computer subsystem: UEFI, drivers, operating systems, browser ... Read more
-
CrowdStrike.com
Preventing Container Escape Attempts with Falcon Cloud Security's Enhanced Runtime Capabilities
Container escape represents one of the most significant security threats in modern cloud computing environments. This allows attackers to break free from container isolation mechanisms, potentially le ... Read more
-
Kaspersky
Exploits and vulnerabilities in Q1 2025
The first quarter of 2025 saw the continued publication of vulnerabilities discovered and fixed in 2024, as some researchers were previously unable to disclose the details. This partially shifted the ... Read more

-
Kaspersky
Exploits and vulnerabilities in Q4 2024
Q4 2024 saw fewer published exploits for Windows and Linux compared to the first three quarters. Although the number of registered vulnerabilities continued to rise, the total number of Proof of Conce ... Read more

-
Kaspersky
Exploits and vulnerabilities in Q2 2024
Q2 2024 was eventful in terms of new interesting vulnerabilities and exploitation techniques for applications and operating systems. Attacks through vulnerable drivers have become prevalent as a gener ... Read more
The following table lists the changes that have been made to the
CVE-2022-0847 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Nov. 06, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-0847 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-0847 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-0847 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-0847 -
Modified Analysis by [email protected]
Jul. 30, 2025
Action Type Old Value New Value -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jul. 30, 2025
Action Type Old Value New Value Removed CWE CWE-665 -
Modified Analysis by [email protected]
Apr. 08, 2025
Action Type Old Value New Value -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Feb. 04, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-665 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/166229/Dirty-Pipe-Linux-Privilege-Escalation.html Added Reference http://packetstormsecurity.com/files/166230/Dirty-Pipe-SUID-Binary-Hijack-Privilege-Escalation.html Added Reference http://packetstormsecurity.com/files/166258/Dirty-Pipe-Local-Privilege-Escalation.html Added Reference http://packetstormsecurity.com/files/176534/Linux-4.20-KTLS-Read-Only-Write.html Added Reference https://bugzilla.redhat.com/show_bug.cgi?id=2060795 Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-222547.pdf Added Reference https://dirtypipe.cm4all.com/ Added Reference https://psirt.global.sonicwall.com/vuln-detail/SNWLID-2022-0015 Added Reference https://security.netapp.com/advisory/ntap-20220325-0005/ Added Reference https://www.suse.com/support/kb/doc/?id=000020603 -
Modified Analysis by [email protected]
Jul. 02, 2024
Action Type Old Value New Value Changed Reference Type http://packetstormsecurity.com/files/176534/Linux-4.20-KTLS-Read-Only-Write.html No Types Assigned http://packetstormsecurity.com/files/176534/Linux-4.20-KTLS-Read-Only-Write.html Third Party Advisory, VDB Entry Changed CPE Configuration AND OR cpe:2.3:h:siemens:scalance_lpe9403:-:*:*:*:*:*:*:* OR *cpe:2.3:o:siemens:scalance_lpe9403_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 2.0 AND OR *cpe:2.3:o:siemens:scalance_lpe9403_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 2.0 OR cpe:2.3:h:siemens:scalance_lpe9403:-:*:*:*:*:*:*:* Changed CPE Configuration AND OR cpe:2.3:h:sonicwall:sma1000:-:*:*:*:*:*:*:* OR *cpe:2.3:o:sonicwall:sma1000_firmware:*:*:*:*:*:*:*:* versions up to (including) 12.4.2-02044 AND OR *cpe:2.3:o:sonicwall:sma1000_firmware:*:*:*:*:*:*:*:* versions up to (including) 12.4.2-02044 OR cpe:2.3:h:sonicwall:sma1000:-:*:*:*:*:*:*:* -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
Jan. 12, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. http://packetstormsecurity.com/files/176534/Linux-4.20-KTLS-Read-Only-Write.html [No types assigned] -
CVE Modified by [email protected]
Nov. 07, 2023
Action Type Old Value New Value Removed CWE Red Hat, Inc. CWE-281 -
Modified Analysis by [email protected]
Dec. 09, 2022
Action Type Old Value New Value Changed Reference Type https://cert-portal.siemens.com/productcert/pdf/ssa-222547.pdf No Types Assigned https://cert-portal.siemens.com/productcert/pdf/ssa-222547.pdf Third Party Advisory Changed Reference Type https://psirt.global.sonicwall.com/vuln-detail/SNWLID-2022-0015 No Types Assigned https://psirt.global.sonicwall.com/vuln-detail/SNWLID-2022-0015 Third Party Advisory Added CPE Configuration AND OR *cpe:2.3:o:netapp:h300s_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h300s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h500s_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h500s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h700s_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h700s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h300e_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h300e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h500e_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h500e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h700e_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h700e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h410s_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h410s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:netapp:h410c_firmware:-:*:*:*:*:*:*:* OR cpe:2.3:h:netapp:h410c:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:siemens:scalance_lpe9403_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 2.0 OR cpe:2.3:h:siemens:scalance_lpe9403:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:sonicwall:sma1000_firmware:*:*:*:*:*:*:*:* versions up to (including) 12.4.2-02044 OR cpe:2.3:h:sonicwall:sma1000:-:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Aug. 10, 2022
Action Type Old Value New Value Added Reference https://psirt.global.sonicwall.com/vuln-detail/SNWLID-2022-0015 [No Types Assigned] -
CVE Modified by [email protected]
Jun. 14, 2022
Action Type Old Value New Value Added Reference https://cert-portal.siemens.com/productcert/pdf/ssa-222547.pdf [No Types Assigned] -
Modified Analysis by [email protected]
Apr. 04, 2022
Action Type Old Value New Value Changed Reference Type https://security.netapp.com/advisory/ntap-20220325-0005/ No Types Assigned https://security.netapp.com/advisory/ntap-20220325-0005/ Third Party Advisory Changed Reference Type https://www.suse.com/support/kb/doc/?id=000020603 No Types Assigned https://www.suse.com/support/kb/doc/?id=000020603 Third Party Advisory -
CVE Modified by [email protected]
Mar. 25, 2022
Action Type Old Value New Value Added Reference https://security.netapp.com/advisory/ntap-20220325-0005/ [No Types Assigned] -
CVE Modified by [email protected]
Mar. 23, 2022
Action Type Old Value New Value Added Reference https://www.suse.com/support/kb/doc/?id=000020603 [No Types Assigned] -
Initial Analysis by [email protected]
Mar. 10, 2022
Action Type Old Value New Value Added CVSS V2 NIST (AV:L/AC:L/Au:N/C:C/I:C/A:C) Added CVSS V3.1 NIST AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type http://packetstormsecurity.com/files/166229/Dirty-Pipe-Linux-Privilege-Escalation.html No Types Assigned http://packetstormsecurity.com/files/166229/Dirty-Pipe-Linux-Privilege-Escalation.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type http://packetstormsecurity.com/files/166230/Dirty-Pipe-SUID-Binary-Hijack-Privilege-Escalation.html No Types Assigned http://packetstormsecurity.com/files/166230/Dirty-Pipe-SUID-Binary-Hijack-Privilege-Escalation.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type http://packetstormsecurity.com/files/166258/Dirty-Pipe-Local-Privilege-Escalation.html No Types Assigned http://packetstormsecurity.com/files/166258/Dirty-Pipe-Local-Privilege-Escalation.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type https://bugzilla.redhat.com/show_bug.cgi?id=2060795 No Types Assigned https://bugzilla.redhat.com/show_bug.cgi?id=2060795 Issue Tracking, Patch, Third Party Advisory Changed Reference Type https://dirtypipe.cm4all.com/ No Types Assigned https://dirtypipe.cm4all.com/ Exploit, Third Party Advisory Added CWE NIST CWE-665 Added CPE Configuration OR *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.8 up to (excluding) 5.10.102 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.15 up to (excluding) 5.15.25 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.16 up to (excluding) 5.16.11 Added CPE Configuration OR *cpe:2.3:o:fedoraproject:fedora:35:*:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:o:redhat:enterprise_linux:8.0:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_eus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_eus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_ibm_z_systems:8.0:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_ibm_z_systems_eus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_ibm_z_systems_eus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian:8.0:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian_eus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian_eus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time:8:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time_for_nfv:8:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time_for_nfv_tus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time_for_nfv_tus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time_tus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_for_real_time_tus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_aus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_aus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_for_power_little_endian_update_services_for_sap_solutions:8.1:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_for_power_little_endian_update_services_for_sap_solutions:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_for_power_little_endian_update_services_for_sap_solutions:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_tus:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_tus:8.4:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_update_services_for_sap_solutions:8.1:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_update_services_for_sap_solutions:8.2:*:*:*:*:*:*:* *cpe:2.3:o:redhat:enterprise_linux_server_update_services_for_sap_solutions:8.4:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:a:redhat:codeready_linux_builder:-:*:*:*:*:*:*:* OR cpe:2.3:o:redhat:enterprise_linux:8.0:*:*:*:*:*:*:* cpe:2.3:o:redhat:enterprise_linux_eus:8.2:*:*:*:*:*:*:* cpe:2.3:o:redhat:enterprise_linux_eus:8.4:*:*:*:*:*:*:* cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian:8.0:*:*:*:*:*:*:* cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian_eus:8.2:*:*:*:*:*:*:* cpe:2.3:o:redhat:enterprise_linux_for_power_little_endian_eus:8.4:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:a:redhat:virtualization_host:4.0:*:*:*:*:*:*:* OR cpe:2.3:o:redhat:enterprise_linux:8.0:*:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:a:ovirt:ovirt-engine:4.4.10.2:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Mar. 10, 2022
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/166258/Dirty-Pipe-Local-Privilege-Escalation.html [No Types Assigned]